Insecure Direct Object Reference (IDOR) in /viva/update.php allows unauthorized modification of team members' names
Describe the bug
An Insecure Direct Object Reference (IDOR) vulnerability exists in the /viva/update.php file.
An attacker can modify the name field for a user in the team_members table without any authentication, simply by knowing the target username and sending a simple HTTP POST request.
Steps to reproduce:
- Ensure the
team_members table exists in the database and contains a record with username='student01' where the name is initially set to Alice.
- Send the following POST request (using Burp Suite, curl, or Postman):
POST /viva/update.php HTTP/1.1
Host: 127.0.0.1:3000
Content-Type: application/x-www-form-urlencoded
username=student01&name=HACKED
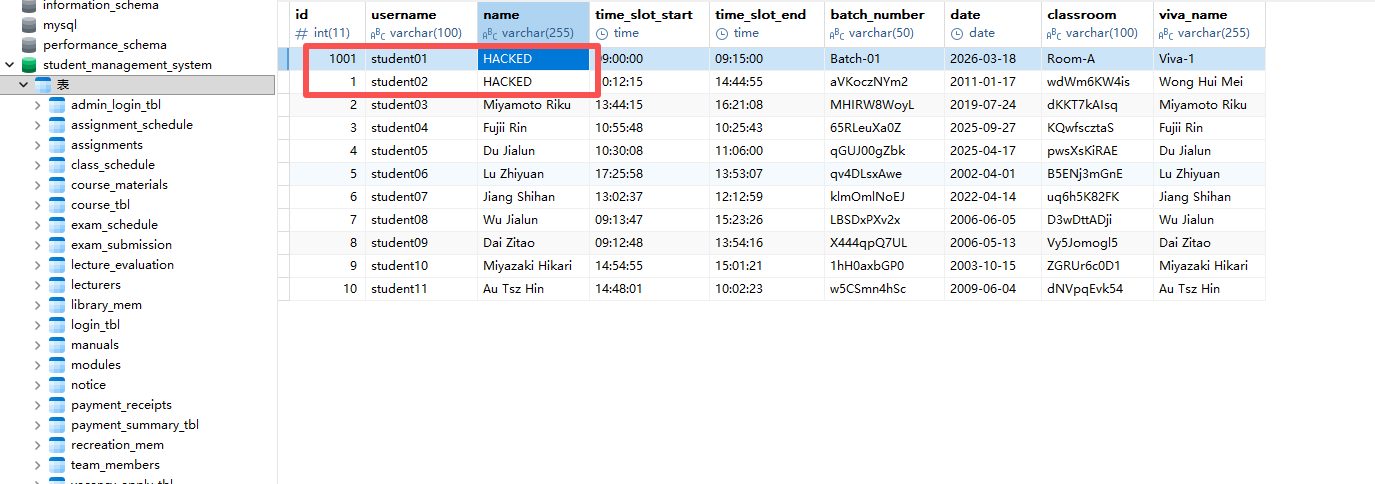
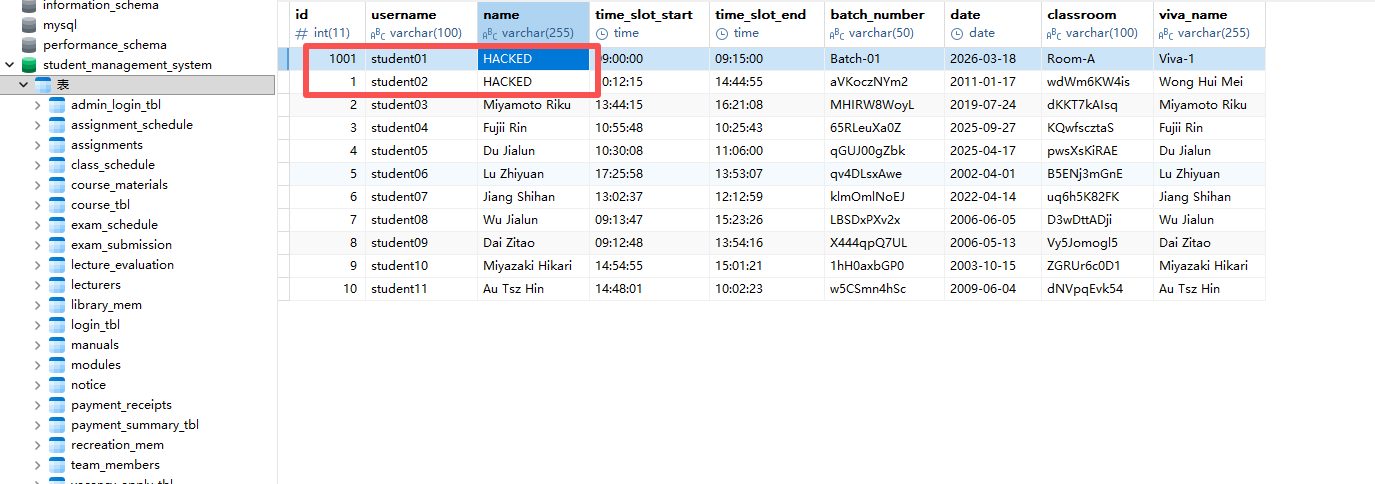
- Query the database again; the
name for student01 will have been changed to HACKED.
- Replace
username with any other existing username (e.g., admin, lec01) – the name for that user will also be modified.
This vulnerability affects all users of the system. Attackers can maliciously alter the name field in team_members for other users (including administrators), potentially causing data inconsistency or enabling further attacks.
Describe the solution
- In
/viva/update.php, first verify that the user is logged in (e.g., by checking session or token).
- Instead of directly using the
username supplied by the client as the update condition, retrieve the current user’s identifier from the session and allow modifications only for their own record.
- If administrator-level modifications are required, implement role‑based access control and ensure that only authorized users can perform such operations.
Suggested fix example:
- Obtain the current username from
$_SESSION['username'] rather than using $_POST['username'].
- Alternatively, if cross‑user modification must be supported, verify that the current user is an administrator and log the operation.
Screenshots

Are you working on it
No
Insecure Direct Object Reference (IDOR) in /viva/update.php allows unauthorized modification of team members' names
Describe the bug
An Insecure Direct Object Reference (IDOR) vulnerability exists in the
/viva/update.phpfile.An attacker can modify the
namefield for a user in theteam_memberstable without any authentication, simply by knowing the target username and sending a simple HTTP POST request.Steps to reproduce:
team_memberstable exists in the database and contains a record withusername='student01'where thenameis initially set toAlice.POST /viva/update.php HTTP/1.1
Host: 127.0.0.1:3000
Content-Type: application/x-www-form-urlencoded
username=student01&name=HACKED
nameforstudent01will have been changed toHACKED.usernamewith any other existing username (e.g.,admin,lec01) – thenamefor that user will also be modified.This vulnerability affects all users of the system. Attackers can maliciously alter the
namefield inteam_membersfor other users (including administrators), potentially causing data inconsistency or enabling further attacks.Describe the solution
/viva/update.php, first verify that the user is logged in (e.g., by checking session or token).usernamesupplied by the client as the update condition, retrieve the current user’s identifier from the session and allow modifications only for their own record.Suggested fix example:
$_SESSION['username']rather than using$_POST['username'].Screenshots

Are you working on it
No