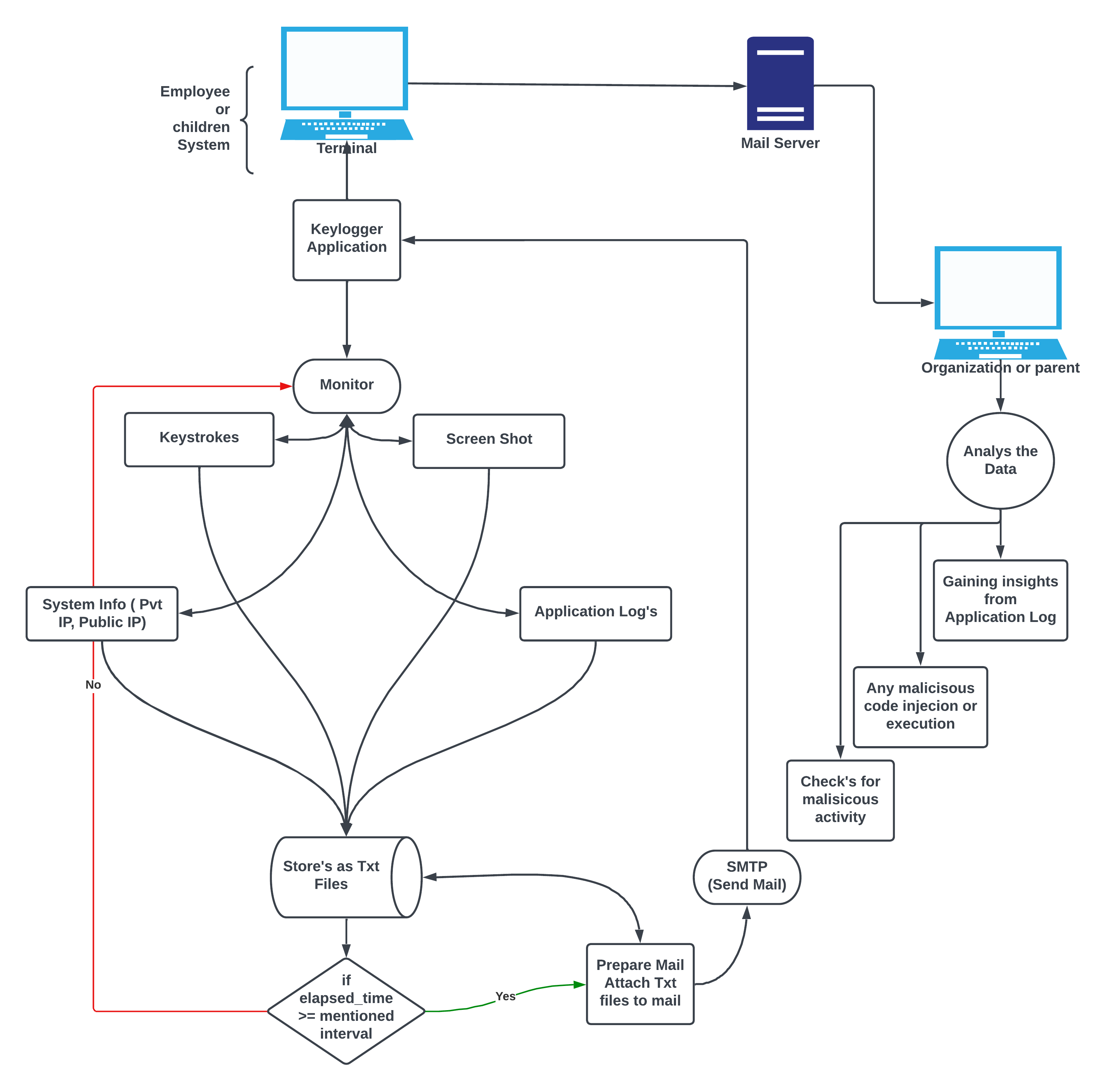
In today's dynamic business landscape, organizations face the constant challenge of securing their sensitive information against cyber threats and data breaches. Our Advanced Keylogger project aims to address this challenge by providing a comprehensive tool for monitoring and detecting suspicious activities within computer systems.
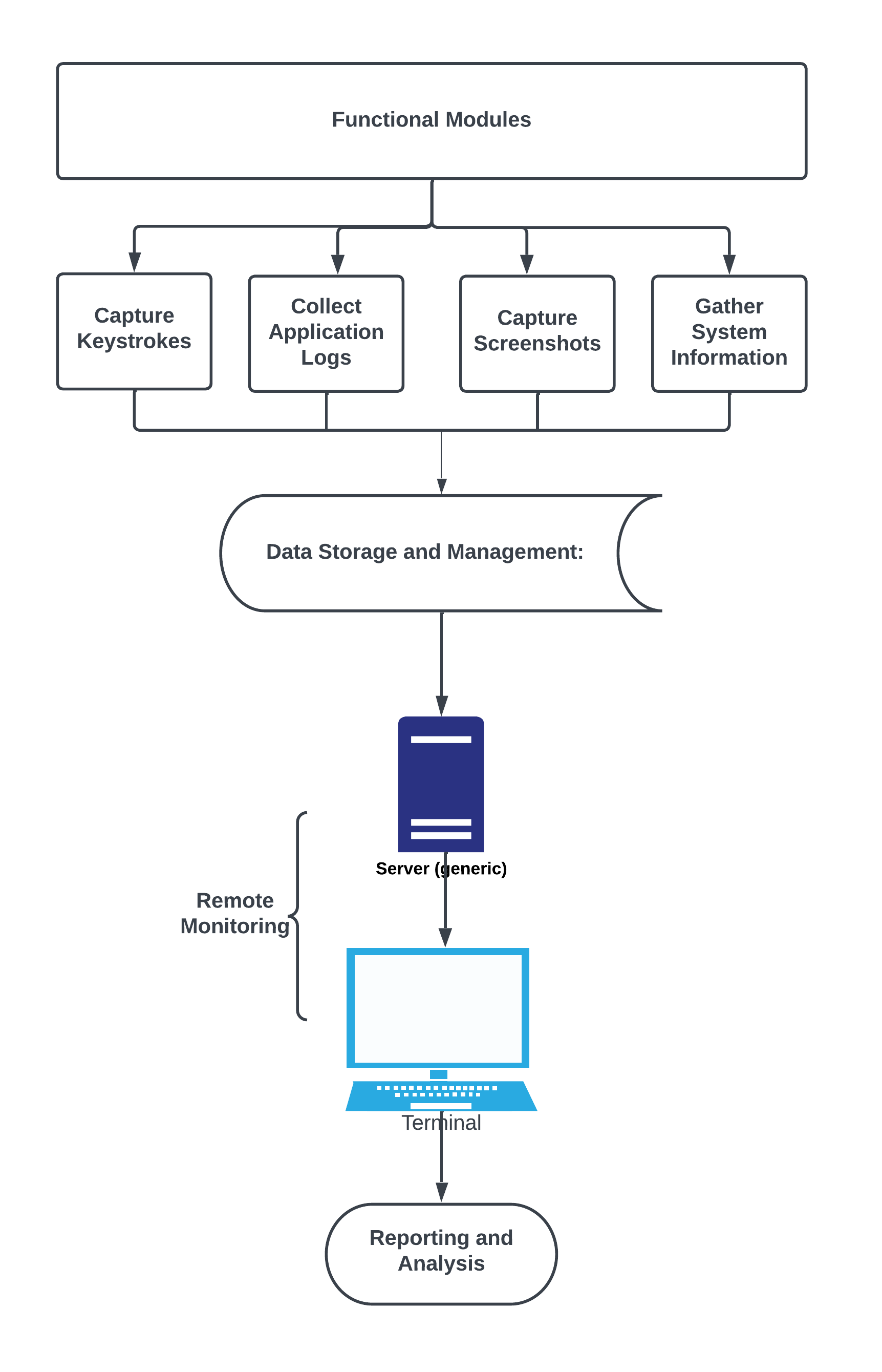
In modern business operations heavily reliant on computer systems, the threat of cyber-attacks is a critical concern. Our Advanced Keylogger serves as a proactive defense mechanism, designed to monitor employee activities and detect potential security threats. It goes beyond traditional keyloggers by capturing various types of information, including keystrokes, screenshots, application logs, and system logs.
- Captures Keystrokes: Our system records keystrokes for detailed analysis.
- Screenshots Capture: Capture screenshots for a visual record of user activity.
- Application Logs: Collect logs generated by applications for comprehensive insights.
- System Logs: Record system logs to analyze system-level activities.
-
Clone the repository:
git clone https://github.com/Krish-Korat/advanced-keylogger.git cd advanced-keylogger -
Install dependencies:
The project relies on the following libraries, which you can install using the provided requirements.txt file:
keyboardsmtplibtimeemailplatformsocketrequestsloggingPIL(Pillow)ospsutilwin32guidatetime
Ensure these dependencies are installed by running the following command:
pip install -r requirements.txt-
Configure the keylogger settings as needed.
-
Run the keylogger:
python keylogger.py- Execute the keylogger on the target machine.
- Monitor logs and alerts through the user-friendly interface.
- Configure real-time alerts and notifications to stay informed about potential security threats.
Ensuring data security and respecting employee privacy are paramount. The Advanced Keylogger project incorporates the following security measures:
- Encryption: Data collected is encrypted to prevent unauthorized access.
- Access Controls: Restricts access to the keylogger to authorized personnel only.
- Privacy Compliance: Adheres to privacy regulations and guidelines to protect employee privacy.
We welcome contributions! Follow these steps to contribute:
- Fork the repository.
- Create a new branch.
- Make your changes and commit them.
- Submit a pull request.