Bluesniff is an open-source Bluetooth Low Energy (BLE) sniffer designed to capture and analyze frequency-hopping traffic using generic Software-Defined Radios (SDRs) like the HackRF One.
Its key feature is the ability to synchronize very quickly (in a few seconds) with an already established BLE connection without having seen the initial CONNECT_IND packet. This makes it useful for passive security audits, long-term monitoring, and protocol reverse engineering.
While dedicated hardware tools like the BTLEJACK excel at intercepting BLE connections, sniffing an ongoing, frequency-hopping connection with a SDR presents unique challenges and opportunities:
- Missing Connection Parameters: Without the initial
CONNECT_INDpacket, crucial parameters like the Access Address (AA), CRCInit, and hopping parameters are unknown. - SDR Latency: The high latency of USB-controlled SDRs makes traditional, reactive frequency hopping impossible. The time to switch frequency is often longer than the interval between packets.
- "Idle" Connections: Many BLE connections are inactive most of the time, only exchanging very short "keep-alive" packets (Empty PDUs). This makes detection very difficult for traditional scanning methods.
Bluesniff tackles these challenges with an innovative, software-defined approach. It attempts to mitigate SDR shortcomings, while exploiting its strengths.
- Firmware-Powered Performance: By implementing a custom, fast Automatic Gain Control (AGC) and a Scheduled Frequency Change mechanism directly into the HackRF firmware, we bypass USB latency and make the SDR responsive enough for BLE.
- Wide-Band Signal Acquisition: Bluesniff can monitor multiple BLE channels simultaneously, increasing the probability of capturing sporadic packets from an unknown connection.
- Hopping State Inference: The core of Bluesniff is a state recovery algorithm. From just a few captured packets, it performs an analysis to reduce the 65,536 possible initial states of the hopping algorithm down to a single, correct one. This allows it to lock onto a connection in a few seconds, even if the connection is completely idle.
- Predictive Tracking: Once locked, Bluesniff predictively schedules frequency changes, allowing the "slow" HackRF to keep up with the fast-hopping BLE protocol.
- Established Connection Sniffing: Recovers all hopping parameters (
Access Address,CRCInit,hopCounter) on the fly. - High-Speed State Recovery: Locks onto idle connections in seconds
- Multi-Channel Monitoring: Leverages the SDR bandwidth to listen on up to 7 channels simultaneously.
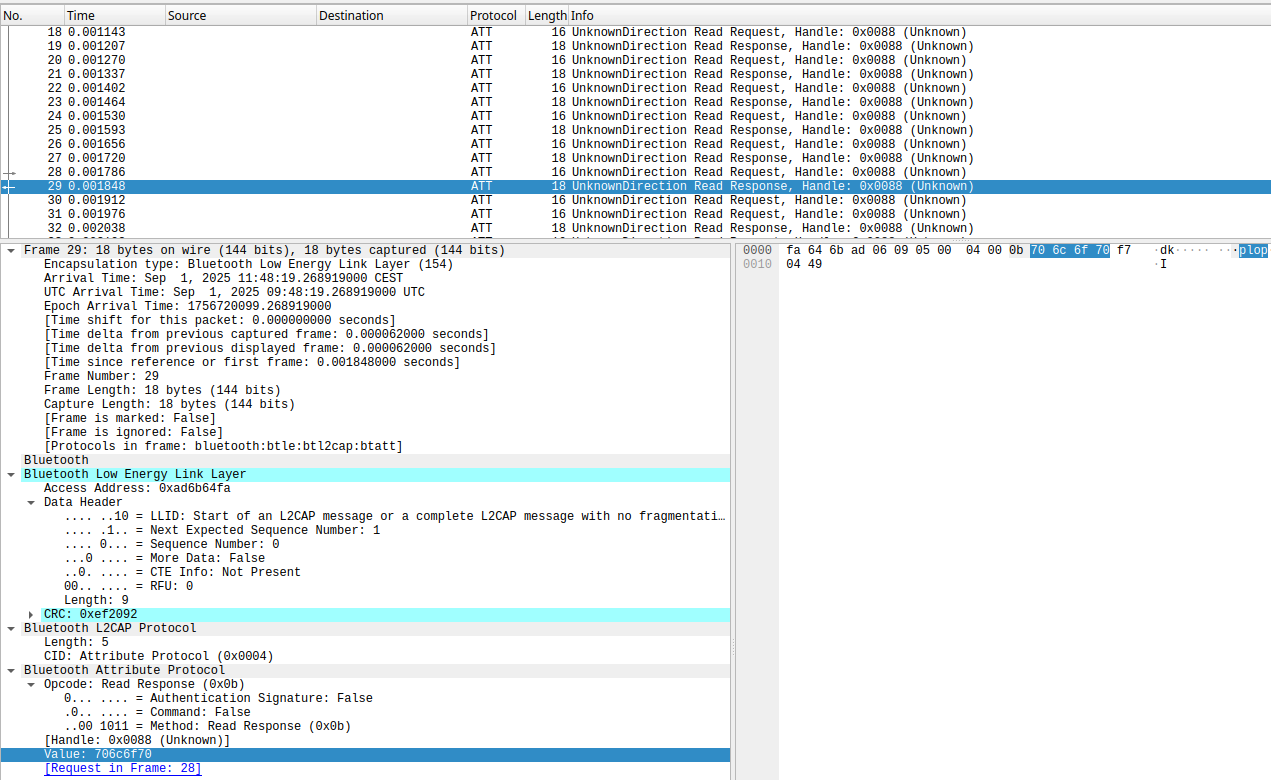
- PCAP Output: Saves captured traffic in a standard
.pcapfile, fully compatible with Wireshark and its Bluetooth LE dissectors. - Custom HackRF Firmware: Includes a patch for the HackRF One firmware to enable high-performance AGC and scheduled frequency changes.
- Live & Offline Analysis: Works with a live HackRF One or can process pre-recorded IQ sample files.
- A HackRF One (or a file with captured IQ samples).
libhackrfinstalled.- A C compiler (gcc/clang) and
make.
To benefit from the fast AGC and scheduled frequency changes, you need to flash the modified firmware onto your HackRF.
- Clone the HackRF source repository. The latest tested version suitable for the patch is the commit id 6aa419f2c001cb431ce262503805098a4f4b44fd
- Navigate to the root directory of the repository.
- Patch the firmware using the provided
firmware.diffpatch:patch -p1 < path/to/firmware.diff - Follow the standard HackRF firmware flashing procedure.
- Recompile and reinstall
libhackrf
WARNING: Flashing custom firmware is at your own risk.
However, in many cases it is possible to recover from a failed firmware update ("unbricking") by using the DFU mode.
git clone https://TODO.git
cd bluesniff/
makeTo sniff a connection around channel 5, capturing 6 adjacent channels, with frequency hopping and AGC enabled and saving the output to a PCAP file:
# -c 5: Center on channel 5
# -W 6: Set a window of 6 additional channels (total 7)
# -o: Enable frequency hopping recovery and tracking
# -p out.pcap: Save decoded packets to out.pcap
# -A: Enable the custom firmware AGC (requires flashed firmware)
# -v: Enable verbose output
./bluesniff -c 5 -W 6 -o -p out.pcap -A -vFull usage help can be obtained with ./bluesniff -h.
The BTLEJACK, by Damien Cauquil, is the gold standard for BLE interception, it leverages dedicated, fast-hopping hardware (nRF5x dongles).
Bluesniff explores a different path. It answers the questions: "What can we achieve on generic, SDR hardware by using more advanced signal processing and algorithmic techniques? What are the pros and cons of using SDR instead of a fully hardware solution?"
Our approach based listening multiple channels at once and infering counter state proves to be particularly effective and fast in the difficult scenario of sniffing an already established connection (even if idle).
This blog post provides an in-depth discussion of the approach.
This project is a proof-of-concept and can be extended in many ways:
-
Adding support for other BLE PHYs (2M, Coded).
-
Implementing automatic recovery of the Channel Map and Connection Interval.
-
Porting the algorithms to other SDR platforms.
-
Developing a hybrid system using an SDR for detection and a dedicated dongle for tracking.
Parts of bluesniff.c are based on the excellent initial work "Bluetooth Low Energy SDR sniffer" by Xianjun Jiao.
The demodulation engine (demod.c), the connection state recovery algorithms, and the HackRF firmware modifications are original contributions of this project.
This project is licensed under the Apache 2.0 License.
